Securing endpoints and network environments has become more challenging than ever. One of the most effective security strategies to protect against malware, ransomware, and unauthorized applications is application whitelisting. This approach involves defining and allowing only approved applications to run on a system, while blocking all other unapproved software. By implementing application whitelisting, organizations can proactively prevent the execution of malicious or unauthorized code, reducing the risk of security breaches and improving overall system integrity.
This guide will walk you through the essential concepts of application whitelisting, its importance in a modern cybersecurity strategy, and how to implement it effectively. You will learn how whitelisting works, its benefits over traditional blacklist-based security approaches, and the best practices for setting up whitelisting policies to protect your devices and networks. We will also delve into the challenges associated with application whitelisting, including compatibility issues and the need for continuous management and updates.
We will introduce you to the best application whitelisting software available today. From enterprise-level solutions to lightweight tools for small businesses, we’ll explore key features, ease of use, and security benefits of leading whitelisting software. By the end of this guide, you will be equipped with the knowledge to choose the right application whitelisting solution for your needs, helping you strengthen your organization’s defenses against emerging cybersecurity threats. Whether you’re a network administrator or a small business owner, this guide will help you secure your environment with the power of application whitelisting.
Here is our list of the best application whitelisting software:
- ThreatLocker EDITOR’S CHOICE This package of system security services is delivered from the cloud and it containerizes all software and files on your system so that malware is blocked from running, applications are given whitelisting approval, and files are protected from unauthorized access. Sign up for a demo.
- ManageEngine Application Control Plus (FREE TRIAL) A “least privilege” package that implements the cloud concept of Zero Trust Access for on-premises endpoints. Runs on Windows Server. Start a 30-day free trial.
- Trellix Application and Change Control This package prevents all but authorized applications from running on a protected device and controls which user accounts can run which applications. Runs on Windows, macOS, Android, and iOS.
- AppLocker This is a feature of Windows and it is integrated into the operating system to control access to applications and files on a computer. It allocates a suite of resources that each user account can run. Integrated into Windows 10 and above and Windows Server 2016 and above.
- Airlock Digital A networked package of units that control user access to applications and data while providing central access to an administrator. Runs on Windows and Linux.
- Faronics Anti-Executable This package creates multiple levels of access to executable files and enables an administrator to allocate these access rights to users. Available for Windows and macOS or as a SaaS package.
The whitelisting software can distinguish between allowed and disallowed applications using various application file and folder attributes such as the file name, file path, file size, digital signature or publisher, and cryptographic hash.
The application of this level of control is one of the modern cybersecurity approaches to prevent several critical threats. Whitelisting is usually enforced at Layer 7 of the OSI model. The purpose of this article is to help organizations understand, evaluate, select, and implement the correct application whitelisting solution for their business.
Why is Application Whitelisting Important?
Nowadays, a signature-based approach to security is no longer considered strong enough to protect systems from modern cyber threats. This is why many organizations embrace the principles of the zero-trust security model in their security strategy. However, the recent malware statistics and cybercrime trends show that they are still a significant problem worldwide. With over 350,000 new malware discovered every day, it’s practically impossible for anti-virus applications to keep tabs on these new and emerging threats. This is where application whitelisting plays a key role.
Application whitelisting is a powerful tool deployed to defend your systems from known and unknown threats such as malware, advanced persistent threats (APTs), fileless attacks, zero-day and ransomware attacks, especially in high-risk environments where maximum security is required. If an application is found to have an unknown reputation, its execution will be denied. The default-deny policy of application whitelisting technologies makes it difficult for zero-day and ransomware attacks to execute.
The scope of application whitelisting doesn’t just end with malware protection. They also provide complete visibility into the applications and processes on your host systems and allow you to monitor changes made to those application files and could either prevent the files from being changed or alert security teams for further investigation. This helps security admins to fine-tune their security policies and update their whitelists accordingly.
So Why is Everyone Not Using Application Whitelisting?
While application whitelisting does a great job of protecting against malicious applications, it can be very restrictive. Every time the user needs to run a legitimate application that is not on the whitelist, they need to contact the admin. This can make a system difficult to use and create operational bottlenecks, inefficiency, and frustration in the workplace, especially in large organizations. In addition, the whitelisting solution can be a massive failure if end users are constantly unable to perform essential business functions on a day-to-day basis.
Creating a comprehensive whitelist and keeping it updated can be quite a challenging and demanding task to handle for the security admin. This explains why most organizations prefer to adopt blacklisting instead of going through the headaches involved in whitelisting. But these headaches can be significantly reduced if the whitelisting solution has pre-existing policy templates or the capability for security admins to pre-approve known applications that are considered safe. Then, when users attempt to install them, it proceeds without any restrictions.
What Does it Take to Successfully Deploy Application Whitelisting Solution?
Application whitelisting solution implementation requires proper planning for a successful deployment. Several best practices should be adhered to during the implementation process. One such is the use of a phased implementation approach— which minimizes unforeseen issues early in the process. The U.S National Institute of Standards and Technology (NIST) framework on application whitelisting recommends the following planning and implementation phases:
- Initiation The purpose of this phase is to identify the current and future needs for application whitelisting through requirements analysis and to determine how those needs can best be met, including a policy document that captures all of those decisions. The outcome of the requirements analysis should help in determining the types of threats the application whitelisting should protect against; the types of applications or application components (executables, libraries, registry entries, configuration files, etc.) that need to be monitored; and the types of application whitelisting that should be used to balance security, usability, and maintainability. At the end of this phase, you should identify a suitable application whitelisting technology that your organization requires.
- Design Once the needs have been identified and the appropriate application whitelisting technologies have been chosen, the next step is to design a solution that meets those needs. Some of the critical design decisions to consider include solution architecture, whitelist management, cryptography policy, and security. If these design decisions are flawed, then the application whitelisting implementation will be more vulnerable to failure.
- Testing After the solution has been designed, the next step is to test a prototype of the design solution to ensure that it meets the design requirements and solution architecture in critical areas such as functionality, management, performance, security, and usability. The testing should be carried out in a test environment before migrating to production systems or servers.
- Deployment Once the testing is completed and all issues are resolved, the next step is to deploy the application whitelisting solution. NIST recommends a gradual rollout of the solution. This provides security administrators an opportunity to measure the impact of the solution and resolve issues before enterprise-wide deployment. It also includes time for the IT staff and users to be trained and become accustomed to the operational lifecycle of the implementation.
- Management After the solution has been deployed, it is now time to manage it throughout its lifecycle. Executing the solution involves operating the application, updating the whitelist, policies, software, and other solution components. Other key activities include patch management, key management, and adapting policies as requirements change. The entire implementation process is repeated when enhancements or significant changes need to be incorporated into the solution.
Evaluating Application Whitelisting Solutions
With various application whitelisting tools out there, choosing the right one for your business and budget can be challenging. What fits perfectly from a price, feature, and functionality standpoint for one project or company may not work for another. Therefore, when evaluating and selecting an application whitelisting solution, you need to ensure that the various functionalities address your security risks and policy requirements. In addition, you don’t want to get caught up in the sales and marketing hype that tends to surround most security products.
It’s crucial to compare competencies in specific product capabilities such as desired features, integration, and product support. Appropriate application whitelisting software features will be critical to a successful deployment. According to NIST, “Organizations should consider application whitelisting technologies already built into the operating system, particularly for centrally managed hosts (desktops, laptops, servers), because of the relative ease and minimal additional cost in managing these solutions. If built-in application whitelisting capabilities are not available or are determined to be unsuitable, then the alternative is to examine third-party solutions with robust centralized management capabilities”. Other key questions to consider when evaluating the effectiveness of potential application whitelisting solutions as recommended in the NIST framework are as tabulated below:
| Key Questions to Consider | Remark |
|---|---|
| How easily can a solution be bypassed? | A solution that can be easily bypassed will make it easier to run unauthorized software, which opens the door to malware |
| How complex is a solution (hash-based versus signature-based, etc.)? | The more complex the solutions, the more challenging for an attacker to circumvent. The downside is that complex solutions may have higher administrative and maintenance overhead |
| What are the relative costs of a solution? | This should include both implementation costs and operational costs of a solution |
| What impact does the solution have on standard performance? | The solution can be a massive failure if the end-users are constantly unable to perform essential business functions on a day to day basis |
| What impact does the solution have on business/mission? | Consider the impact of risk associated with false positives and false negatives |
| How usable is the solution for both users and administrators? | A great solution will strike a balance between usability and security while balancing the budget |
| What are the long-term maintenance demands for running the solution? | This is important, considering the significant costs associated with maintenance. The amount of maintenance needed must be balanced with the effectiveness of the solution. |
Table 1.0 Key considerations when evaluating potential whitelisting solutions
The best Application Whitelisting solution
Our methodology for selecting application whitelisting software
We reviewed the market for application whitelisting systems and analyzed the options based on the following criteria:
- A service that can block unauthorized software
- An access control system that provides a number of levels of access
- An access rights manager that maps user accounts to access levels
- Control over access to files and other data sources
- An Administrator account that is able to set up and manage access controls and rights
- A free trial or a demo account for a risk-free assessment opportunity
- Value for money from a service that is able to both block malware and prevent intruder manipulation of authorized applications.
1. ThreatLocker (ACCESS FREE DEMO)
ThreatLocker is a platform of resource protection systems that create a Zero Trust Architecture. The Whitelisting unit is called Allowlisting. This is a method of blocking all of the software on a computer from running unless it has been specifically approved. The Allowlisting method blocks malware and ransomware by default.
Key Features:
- Blocks all software by default
- Prevents unauthorized software
- Disables ransomware
- Part of a platform of security services
Why do we recommend it?
ThreatLocker blocks all processes from running on a computer. The administrator then users up a whitelist and software on that list is able to run. This is called Allowlisting and one list can be shared among multiple endpoints. ThreatLocker enables you to build a Zero Trust Architecture.
The strategy behind the ThreatLocker system is that all software is prevented from running. This closed security stance means that you don’t need to worry about users installing unauthorized software or malware and ransomware sneaking onto your company’s computers. Executable files will never activate unless you list them in your ‘allowlist’.
ThreatLocker also provides a form of access rights management in its package. This can apply controls on access to resources to specific IP addresses and allow or block users from having access to USB devices.
The entire package of the ThreatLocker platform enables you to move to protecting applications rather than networks or computers. This means that those applications can be hosted anywhere, including on your site or on cloud platforms. The deactivation of all execution rights for any file on your computers means that you could accumulate quite a lot of useless dead software on your endpoints and so you will need to institute a regular admin task to clean up each device. However, it is better to have dead-weight than active ransomware on your system.
The Allowlist system includes a Learning Mode option. This process takes about a week and it lets the access control service work out by itself which software and services are regularly used on each device. Although this process is a time-saver for busy administrators, the resultant list will still need to be checked before it is accepted because the ThreatLocker system doesn’t take software license ownership into account.
Who is it recommended for?
This is a sleek solution for any business. It is very easy to install and set up, so you don’t need to have cybersecurity expertise to get failsafe protection against viruses and ransomware. It is also available in a version for managed service providers.
Pros:
- Easy to implement
- Introduces automation into ZTA migration
- Allow listing interacts with other modules
- Provides protection against ransomware attacks
- Focuses security on applications
Cons:
- Doesn’t include a full access rights manager
ThreatLocker is a cloud service, which makes it easy to sign up for. You will need to download an agent program onto each endpoint but that process is guided and launched from the ThreatLocker dashboard. Access a demo to find out more about the ThreatLocker system.
EDITOR'S CHOICE
ThreatLocker is our top pick for an application whitelisting system because it offers an easy way to transition to Zero Trust Architecture and even includes a discovery service that works out which software your users regularly access on all of your endpoints. This system prevents any software package from executing unless you specifically approve it in a whitelist, which is called an ‘Allowlist’ in the ThreatLocker terminology.
Download: Access a demo
Official Site: https://threatlocker.com/demo-sign-up
OS: Cloud-based
2. ManageEngine Application Control Plus (FREE TRIAL)
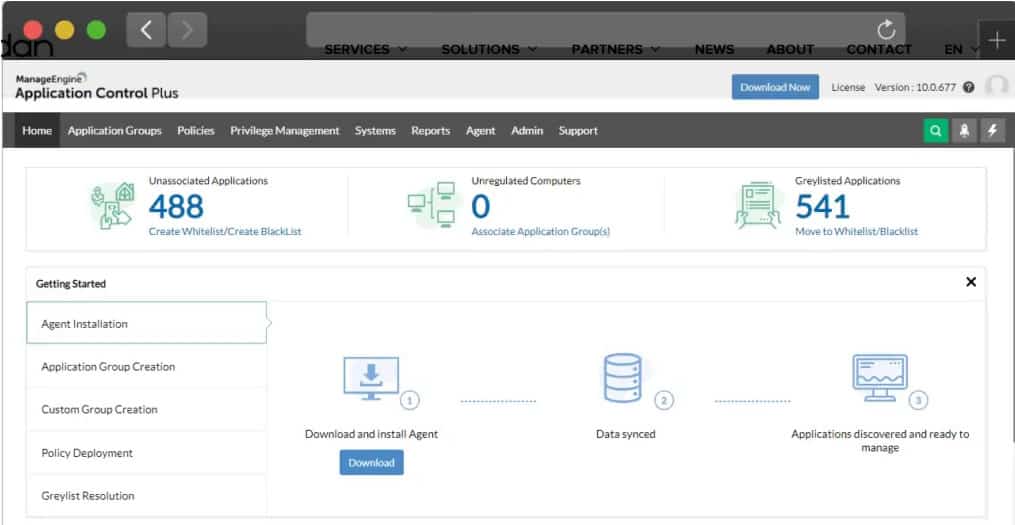
Application Control Plus software is an on-premises solution that combines Least Privilege and Zero Trust principles to enable organizations to automate the application whitelisting process. Controls fence applications individually, fencing them and allowing only authorized access to them and their related privileges.
The Application Control Plus system is implemented in two modules, a controller (server) and an endpoint agent (client). Agents scan every endpoint within a LAN and provide a list of the applications installed in them, along with details of all their executables. This helps organizations enforce policies to control and authorize application access, prevent malware threats, and tackle productivity loss.
Key Features:
- Centralized controls
- Autodiscovery
- Access controls per application
Why do we recommend it?
Application Control Plus is ManageEngine’s entry into the Zero Trust Architecture field. The package implements an allowlisting policy, which is very similar to the ThreatLocker system. This package is an on-premises package with a server unit that reaches out to endpoint agents across the network.
Whitelists are implemented as application rules, which are set up for each authorized application rather than for the entire endpoint. The system automatically blacklists unauthorized applications because nothing outside of the application control system is allowed access to the operating system. As well as blocking users from installing their own software, this feature completely blocks malware installation attempts.
Centralized administration for all endpoints blocks local Admin accounts, removing the ability of users, intruders, or malware from getting into the controls of the device.
While one side of the system fences applications, the other aspect of access controls manages user accounts. Each account has an access level assigned to it and these specifications cannot be elevated to system privilege at will by the user.
A stop-gap status for privilege management and access rights allows short-term access to a new application under study. These can be end-dated to prevent absent-minded administrators from allowing these short-term permissions to roll on indefinitely.
The predefined rules that are available within the administrator console of Application Control Plus give a system manager a quick solution to setting up workable application controls while getting to know the system. These can be fine-tuned through customization later.
Who is it recommended for?
This system is a little more complicated than the threatLocker strategy because it includes locks on the system account on each endpoint – some processes require elevated access to run. There is a Free edition to manage up to 25 endpoints and the paid plan includes a WAN option.
Pros:
- Creates a virtualization/container for each application
- Everything outside of approved applications is blocked from accessing the operating system
- Autodiscovery and preset rules provide quick solutions to get application controls operating quickly
Cons:
- Doesn’t extend to cloud services
The controller for ManageEngine Application Control Plus runs on Windows Server and endpoint agents are available for Windows and macOS. There is a Free version of the software that is limited to monitoring up to 25 devices. A fully functional free 30-day trial is available for download. The licensing model is based on an annual fixed-cost subscription including support or a one-time (perpetual) license fee + yearly maintenance cost (AMS).
3. Trellix Application and Change Control

Trellix Application and Change Control software is a centrally managed whitelisting solution that prevents zero-day and APT attacks by blocking the execution of unauthorized applications on servers, corporate desktops, and fixed-function devices such as point-of-sale (POS) and customer service terminals. Trellix Application and Change Control uses dynamic whitelisting to ensure that only trusted applications are allowed to run. This provides IT with visibility and control over clients and helps enforce software license compliance.
Key Features:
- OS access only for approved software
- Automatic malware blocking
- Automated approval rules
Why do we recommend it?
Trellix Application and Change Control is the new name for McAfee Application Control. It implements whitelisting for endpoint protection with blocks on all software that isn’t in the allow-list. The package also searches each endpoint and generates a list of the software that each holds. The administrator console is hosted in the cloud.
The McAfee system examines all executable files and lists them for controls. Anything not allocated controls in the management console is excluded from the operating system. These controls extend to binaries, kernel components, DLLs, ActiveX controls, scripts, and Java components.
Time-pressed administrators will appreciate the dynamic whitelisting function in the management console. This allows certain applications to be instantly approved without manual intervention through a set of rules, for example, a business might decide not to waste time evaluating the security risk of installing Microsoft products.
Where approvals are fast-tracked, a specific default user group is permitted access to it. This privilege can be associated to specific groups, leaving the administrator the decision over whether to permit access to the new application to other groups as well.
The Trellix Application and Change Control system will integrate with your patch manager, letting you maintain your regular patch cycles. This prevents whitelisted applications from being exploited via memory buffer overflow attacks on Windows 32- and 64-bit systems.
The McAfee system also includes an option notification system, which presents explanations to users on why they are blocked from installing software on their workstations or what steps they need to go through in order to gain access to a permitted package from which they are currently blocked.
Who is it recommended for?
The Trellix platform provides a range of products for system security and the Application Control product is just one of them. The tool is most effective when used in conjunction with a complete protection strategy, which requires planning. This is a strategy that is most suitable for large organizations.
Pros:
- A fast-track approvals automation stream
- User information popups
- Strong blocks on operating system access
Cons:
- Use approval automation with caution
Register for access to a free demo to assess the Trellix system.
4. AppLocker

AppLocker is an application whitelisting technology from Microsoft. It is included with enterprise-level editions of Windows 10 and 11, including Windows 10 Education and Enterprise Edition, and Windows Server 2016, 2019, and 2022 editions. Unfortunately, AppLocker is not supported on Windows 10 Home and Professional Edition.
Key Features:
- Built into Windows
- Controls operating system access
- Blocks unauthorized executables
- Automatic access permission
- Allows unrestricted access to authorized users
Why do we recommend it?
AppLocker is a similar solution to the threatLocker system. All programs are blocked unless they are on a whitelist. This solution comes from Microsoft and is only available for Windows and Windows Server. One problem with this tool is that it won’t block software running under the system account.
AppLocker allows security administrators to restrict which programs users can execute based on the program’s path, file name, publisher, or hash. As a result, AppLocker is ideal for organizations that currently use Group Policy to manage their PCs. It automatically whitelists internal Windows applications, making the user experience less complicated.
Microsoft recommends the following scenarios as ideal for the use of AppLocker:
- Your organization’s security policy dictates the use of only licensed software, so you need to prevent users from running unlicensed software and restrict licensed software to authorized users.
- Your organization no longer supports an appIn addition, so you need to prevent it from being used by everyone.
- The potential that unwanted software can be introduced in your environment is high, so you need to reduce this threat.
- The license to an app has been revoked, or it is expired in your organization, so you need to prevent it from being used by everyone.
- A new app or a new version of an app is deployed, and you need to prevent users from running the old version.
- Specific software tools are not allowed within the organization, or only specific users should access those tools.
- A single user or small group of users needs to use a specific app that is denied for all others.
- People share some computers in your organization with different software usage needs, and you need to protect specific apps.
Notwithstanding, anyone with admin rights to their local device can be able to subvert AppLocker policies. AppLocker can also be easily bypassed using techniques such as:
- Writing an unapproved program to a whitelisted location
- Using a whitelisted program as a delegate to launch an unapproved program
- Hijacking the DLLs loaded by a trusted application in an untrusted directory
Who is it recommended for?
AppLocker is free if you have the right versions of Windows and Windows Server. So, this is suitable for businesses that only run Windows on their endpoints. The computers of remote workers that are user-owned are harder to deal with because those owners will be able to use the system account where AppLocker does not function.
Pros:
- Free to use for Windows devices
- Offers a central controller account for multiple endpoints
- Ties into access rights management
- Prevents users from installing software
- Protects the kernel
Cons:
- Only operates on Windows
- Can be bypassed programmatically
Overall added AppLocker to this list because it is built into Windows and so is integrated into the consoles that systems administrators currently use and understand. By controlling application access to the operating system, this tool can easily and efficiently block them from being run by the processor of the protected computer. This is a very effective system protection mechanism.
5. Airlock Digital

Airlock Digital is an Australian-based cybersecurity firm that is focused on addressing application whitelisting challenges. Airlock makes it easy for organizations to create and manage secure application whitelists while providing centralized visibility over all files in dynamically changing computing environments.
Key Features:
- Networked controls
- Blocks on intruder probes
- Emergency bypass
- Blocklisting against attacks
Why do we recommend it?
Airlock Digital is able to block software from running on Windows, macOS, and Linux. The package includes a central console, which provides activity reporting and it can provide compliance enforcement and reporting. While the administrator console is hosted on the cloud, each endpoint gets an agent that implements the blocking technology.
The Airlock Digital system imposes execution controls for all executables, application libraries, installers, and scripts.
The package includes live activity monitoring and presents tools for administrators to take temporary action over permissions to alleviate systemic seize-up or head-off attacks. This supports rapid policy management changes to buy time for longer-term analysis and policy recasting.
Exception handling (bypass) features allow administrators to temporarily exclude devices from whitelisting via Airlock One Time Pad (OTP) functionality to ensure business continuity. It is also possible to create your own custom rules.
Administrators get control over where and how they apply trust-hash, publisher, path, or process. Unique configuration features make it difficult for malicious actors to test and validate their attacks.
- Airlock Server—Installed on servers (physical or virtual)
- Airlock Enforcement Agent—Installed on workstations and servers to provide protection
- Airlock Application Capture (optional)—Installed on a known trusted workstation or server to assist with maintaining Application Whitelisting rule sets.
You can request a personalized demo to enable you to get a feel of the software before making financial commitments.
Who is it recommended for?
Airlock Digital is a good choice for any business. It is able to protect endpoints wherever they are and it is very easy to set up, so small businesses running virtual offices would really benefit from this package. The tool provides compliance reporting for HIPAA and PCI DSS.
Pros:
- Centralize controls over a fleet of endpoints connected to a network
- Control access to the operating system for software, blocking unauthorized applications
- Emergency workaround to prevent company-wide lockouts
- Confounding strategies to block hackers and intruders
Cons:
- Control workarounds could weaken the security of the service
A fully functional free 30-day trial is available for download. The licensing model is based on an annual fixed cost subscription including support or a one-time (perpetual) license fee + yearly maintenance cost (AMS).
6. Faronics Anti-Executable

Faronics Anti-Executable is a mature whitelisting application that blocks sophisticated threats such as zero-day, APT, and ransomware attacks by ensuring only approved applications run on a computer.
The Faronics package specifically manages operating system access for program files with the .exe, .dll, .com, .scr, .jar and .bat file extensions. This is a permitted virtualization system where only managed applications get access to the operating system to launch. Thus, any software that is installed without going through the stage of being enrolled in the Anti-Executable system simply cannot be run.
Key Features:
- Graded permission levels
- Default permission rules
- Extensive activity logging
Why do we recommend it?
Faronics Anti-Executable is a software-blocking system that is also able to control access to peripheral devices. This system installs on each protected device but you can consolidate controls from multiple devices in a Web-based console. This system is only available for Windows and Windows Server.
To prevent strict controls from preventing the business from operating, there is a graylisting option that can be applied automatically. However, use this feature with caution and only for short-term use to enable software to be assessed before it is fully approved – for example, during a free trial period before buying.
The Faronics system includes a high degree of automation to speed up the administration process. It provides automatic scanning of endpoints that compiles a list of installed software, enabling an administrator to run through the list allowing or blocking each package. This quick-fix solution applies a default rule set, which buys time for detailed investigations before fully approving each package.
User access rights management can be implemented through Active Directory. Permitted applications can be allocated to groups, effectively creating a standard menu of services that can be allocated to each user group.
The system provides extensive activity logging, which includes rollback storage for console or AD changes. These records feed through to compliance reporting.
Faronics Anti-Executable comes in both standalone (on-premise) and cloud editions and is supported on MAC and Windows OS. Windows Server editions of Anti-Executable cannot be installed on a non-server OS. In contrast, non-server editions of Anti-Executable cannot be installed on a server OS. The on-premise and cloud editions are as follows:
- Standard: A single standalone computer loaded with a non-server operating system.
- Server Standard: A single standalone computer loaded with a server operating system
- Enterprise: Multiple computers loaded with non-server operating systems.
- Server Enterprise: Multiple computers loaded with server operating systems
- Faronics Anti-Executable Cloud: Machine learning-assisted application whitelisting
Who is it recommended for?
The Faronics system is modular. You install the software on each protected device. The software is affordable for small businesses. However, larger businesses will find the need to manually install the software on each endpoint a detraction. Its limit to managing only Windows will also be a problem for some.
Pros:
- Autodiscovery and software inventory creation
- Quick graylisting for short-term access allowance
- Mass approvals for trusted software brands
Cons:
- Graylisting could be abused to defer decision making
A fully functional free 30-day evaluation version is available for download. A valid license key is required to continue running the application afterward.
Application Whitelisting FAQs
Why is application whitelisting important?
Application whitelisting is a replacement for the traditional approach of allowing the user access to an endpoint and then installing antivirus systems on each machine to block unauthorized software. Application whitelisting combines access rights management with software inventory control. Each application is fenced with independent access lists and only those protected applications are approved for access to the operating system. Without access to the services of the operating system, executables cannot run. Therefore, all software that is installed surreptitiously is useless and can do no harm.
How is application whitelist implemented?
If you manage cloud assets and have been implementing Zero Trust Access for them, you will immediately understand how application whitelisting operates. This is the on-premises version of ZTA. All software is blocked by default from getting access to the operating system. When enrolled in the whitelist, all access to that application is blocked by default. Users are then allowed in on an application-by-application basis, either individually, or through a user group.
What is the difference between application whitelisting and blacklisting?
Application whitelisting blocks all software from running and then an administrator adds each package to an approved list, which enables it. Blacklisting operates in an environment where all software is allowed to run except for those packages that have been specifically named.





